Original Link: https://www.anandtech.com/show/8993/lenovo-superfish-and-security
Lenovo, SuperFish and Security
by Ian Cutress on February 19, 2015 6:55 PM EST
For the many of us that have purchased a laptop, we are somewhat used to the amount of bloatware that comes pre-installed. Most of this relates to the company specific software, or free trials for office applications or anti-virus software. I would imagine that the more technologically savvy users uninstall some of this bloat for themselves and their family and friends, but it does give an opportunity for the manufacturer to install what they want before the device gets shipped.
Here at AnandTech we receive laptops on a regular basis for review, and where we can we tend to ask for retail units so we can analyze the hardware without fear of getting a ‘review-focused’ sample. The same thing goes for motherboards, SSDs, and graphics cards, which also come with their own software but the user has to specifically install everything. With a laptop, smartphone, tablet, workstation, or notebook, it all comes pre-prepared for the user to plug and play. The demand to remove the bloatware has led to smartphones and tablets being offered with pure stock versions but also carrier customized ones, and some users get the choice of both.
A topic that has been in the news today, and whose symptoms date back a little further, has been with Lenovo laptops and notebooks. This software is called SuperFish and comes as a browser add-on, which Lenovo calls a ‘Visual Discover’ program that detects when a website has advertising and replaces it with targeted images based on what the user is looking at in order to make informed choices at potentially lower prices. This comes with a variety of issues.
First, it replaces the advertisement(s) on the website, which offers the website a form of income (such as AnandTech and other advertiser driven models). The new advertisement redirects the link to a server that may benefit Lenovo, distorting the ad views for that particular website and shifting income back to the laptop manufacturer.
Second, SuperFish is actively scanning the websites that people look at, resulting in privacy issues. Lenovo has stated that this software analyzes images in an algorithmic pattern (presumably similar to Google Goggles) rather than tracking the behavior of the user, but without access to the code most users will still not trust the software. After consistent issues regarding security and tracking in the media recently, especially with certain ‘Smart TVs’, it is understandable how users are concerned over devices that do not respect their privacy.
Third, the best explanation for SuperFish comes down as adware. Malware and adware have been a common threat of the century when it comes to web browsing, where software places unwanted advertisements in the eye-line of the user to generate revenue. If we take that definition then SuperFish falls under that category, no matter how it is dressed up.
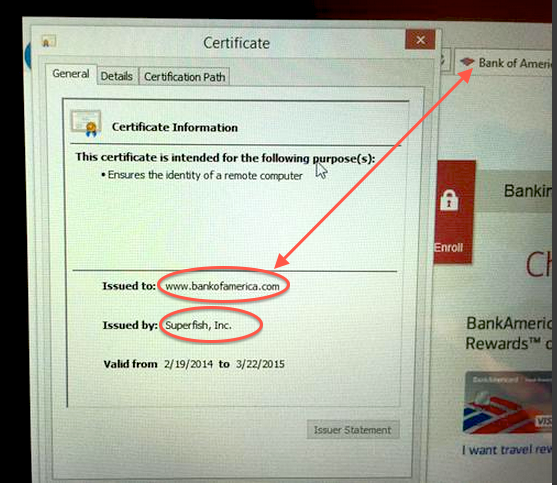
The fourth issue (and arguably most severe issue) revolves around security. This is twofold – the SuperFish software will intercept any HTTPS encrypted webpage that has advertisements when it replaces them with its own, creating a mix of secure and insecure content. This allows other software to come in and potentially inject its own attack, stealing sensitive information. The second issue with security is that SuperFish issues its own SSL certificates for a large number of common sites, with severely reduced security than what is often required, such as with banks with the example that is circling the internet:
This essentially amounts to a fake root certificate, necessary for SuperFish to intercept HTTPS connections to do its image analysis, but in the process giving SuperFish access any information passed via HTTPS. Any and all alarm bells should be ringing in everyone’s ears at this point, as this means the SuperFish software has the means to see bank information, personal information, and any other sensitive information. These certificates are accepted because Lenovo has pre-installed the PC with details to accept SuperFish certificates, essentially creating a 'self-signing authority'.
But most damaging of all is the potential for these certificates to be used by malicious third parties. As it turns out, the security of these certificates would seem to be using SHA-1, which is insecure and can be overcome with the right software and ordinary computing hardware. The 1024-bit RSA key has also been cracked, with the private key being bundled with the software in order to execute on-the-fly digital certificate signing. Consequently researchers have already cracked the key and password with relatively little effort, exacerbating the scale of the situation. Easily repeatable by hackers, this would allow a hacker to come in and use the same password/key combination to sign their own fake SSL certificates against the SuperFish root certificate, in essence allowing anyone with network contol to execute a man-in-the-middle attack on any Lenovo system with the SuperFish root certificate installed.
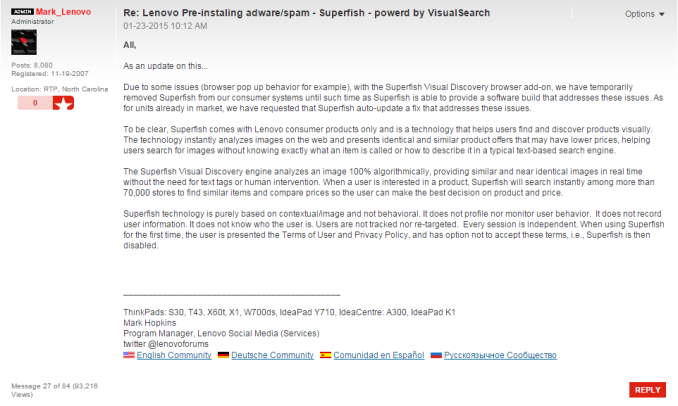
The reason this situation has come to the forefront today is due to a tweet on Wednesday by the co-director of the Open Crypto Audit Project and a single forum post by a Lenovo employee, describing how SuperFish works:
Despite whatever good intentions Lenovo had behind the software, the implementation as well as the execution leave a lot to be desired, especially in a climate where security and privacy are key factors with their main user demographic. I doubt that any such software would ever been considered in this digital age as viable, unless it was forced upon a user at a work machine to only ever be used for that purpose. But for home users, this post waves a black flag followed by a red one – the race is being stopped and you are being disqualified.
There are two elements to this story from Lenovo. Perhaps understandably, the forum post mentions that SuperFish is currently disabled on Lenovo’s end. However, the software is still present on the user machines and most importantly the weak root certificate is still installed.
The next is an official response from Lenovo on SuperFish, which you can read here. A brief summary is included here:
- SuperFish was previously included in some consumer notebooks shipped between September and December 2014.
- User Feedback was not positive.
- SuperFish has been disabled server-side since January.
- Lenovo stopped preloading the software in January.
- Lenovo will not preload this software in the future.
- Lenovo is providing support on its forums for any user with concerns. If users still wish to take further action, detailed information is available here.
As noted, the response from the community about SuperFish has been negative. Marc Rogers writes a particularly scathing post about the situation, and mainstream media such as the BBC is actively picking up on the issue. Over 30 models are affected by this software, all of which are noted in the official Lenovo response, and details are provided on how to remove the software. If you think you are affected, @FiloSottile is hosting a SuperFish detector at https://filippo.io/Badfish/. There are also extra instructions to remove malicious certificates from a system at the bottom of the page here.
Lenovo has stated that new units are no longer preloaded with SuperFish. However, there are most likely units still in the supply chain from before January that have the software. Lenovo is issuing an update to SuperFish to disable itself if the user accepts the user agreement on first use.
The end result is that this comes at the expense of Lenovo’s reputation. As a brand that has made it into most of the largest markets around the world, there’s an element of trust that takes years to build and a single action to erode. I suspect there will be some calls for investigations or forms of compensation, and at this point it is difficult to estimate if any legal action will be sought or anything illegal can be proven due to compromised systems. Lenovo at this time is treading carefully, only providing an official statement on the issue despite the initial furor caused over a single forum post that has now been viewed over 100,000 times.
I’m sitting at my work desk with a Core-M based Yoga 3 Pro and fortunately it is not one of the models affected. Loading up a detection website confirms this. Normally on AnandTech our testing is directed mostly at the hardware, the performance and the design choices made, but rarely the politics. It is a difficult subject for a website like AnandTech to tackle, and given the amount of information around, it is important to stick to the facts here. There has already been a backlash over social media about SuperFish, and Lenovo has acted quickly. Some users will be expecting an apology, rather than the attempted justification, and we will have to see how this situation develops. I can imagine Lenovo not stating anything except through official channels for a while. They will be presenting and have a booth at Mobile World Congress in March, so we may (or may not) see any development then.
Sources: Lenovo, Marc Rogers, Errata Security, @FiloSottile
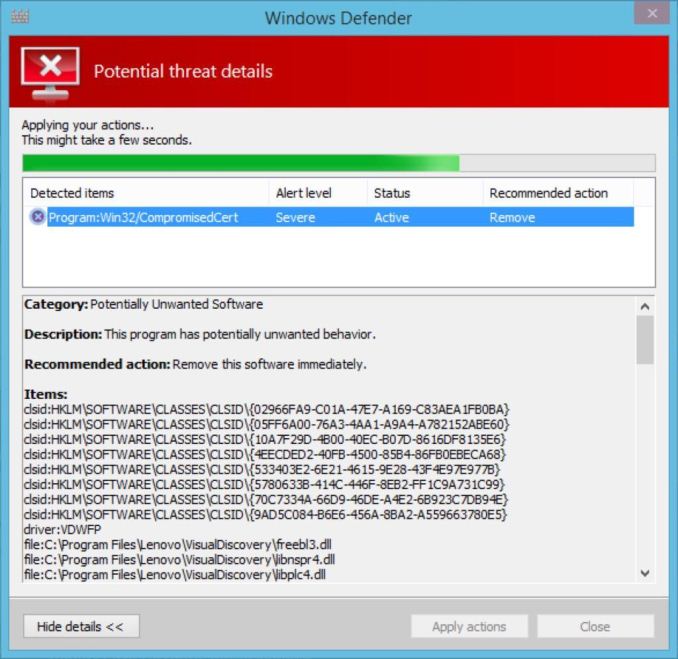
Update 2/20: It is now being reported that Windows Defender is taking a grim view of SuperFish and knocking it out of the frying pan and into the fire. Anyone for baked cod? Defender will now remove SuperFish as well as the installed certificate authority and the certificates still on the system. @FiloSottile has screenshots showing Defender in action:
Update 2/23: Lenovo has now launched its own tool for removing SuperFish and all certificates for major browsers. Also available is the source code for the software, and manual instructions for users who do not wish to install the tool. I can all be found here.